May 25, 2026 3 min read
by Peter Humaj
Read
More
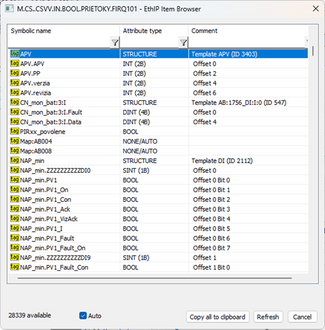
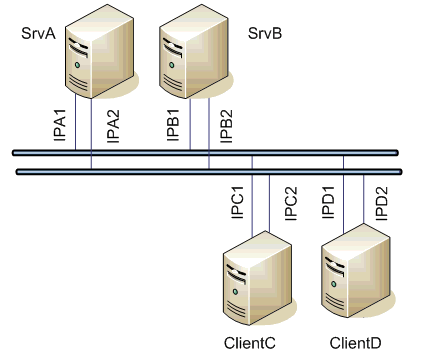
Communication - S7-200
How to establish communication between S7-200 and Ipesoft D2000 using the ACCON-NetLink-PRO compact converter.